Valid SC-200 Dumps shared by ExamDiscuss.com for Helping Passing SC-200 Exam! ExamDiscuss.com now offer the newest SC-200 exam dumps, the ExamDiscuss.com SC-200 exam questions have been updated and answers have been corrected get the newest ExamDiscuss.com SC-200 dumps with Test Engine here:
Access SC-200 Dumps Premium Version
(370 Q&As Dumps, 35%OFF Special Discount Code: freecram)
<< Prev Question Next Question >>
Question 90/171
You are configuring Microsoft Cloud App Security.
You have a custom threat detection policy based on the IP address ranges of your company's United States-based offices.
You receive many alerts related to impossible travel and sign-ins from risky IP addresses.
You determine that 99% of the alerts are legitimate sign-ins from your corporate offices.
You need to prevent alerts for legitimate sign-ins from known locations.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
You have a custom threat detection policy based on the IP address ranges of your company's United States-based offices.
You receive many alerts related to impossible travel and sign-ins from risky IP addresses.
You determine that 99% of the alerts are legitimate sign-ins from your corporate offices.
You need to prevent alerts for legitimate sign-ins from known locations.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
Correct Answer: A,D
Topic 1, Litware inc.
Existing Environment
Identity Environment
The network contains an Active Directory forest named litware.com that syncs to an Azure Active Directory (Azure AD) tenant named litware.com.
Microsoft 365 Environment
Litware has a Microsoft 365 E5 subscription linked to the litware.com Azure AD tenant. Microsoft Defender for Endpoint is deployed to all computers that run Windows 10. All Microsoft Cloud App Security built-in anomaly detection policies are enabled.
Azure Environment
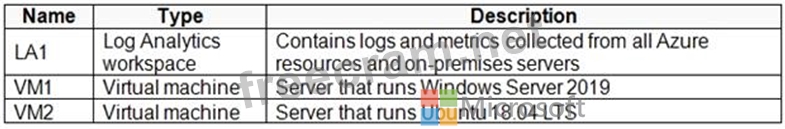
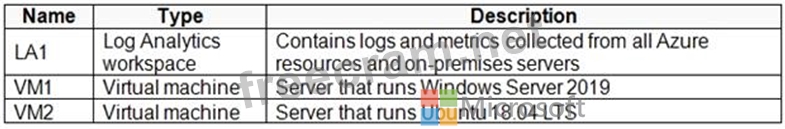
Litware has an Azure subscription linked to the litware.com Azure AD tenant. The subscription contains resources in the East US Azure region as shown in the following table.
Network Environment
Each Litware office connects directly to the internet and has a site-to-site VPN connection to the virtual networks in the Azure subscription.
On-premises Environment
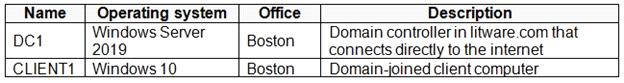
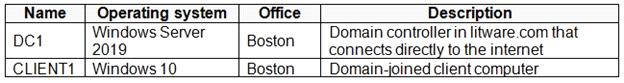
The on-premises network contains the computers shown in the following table.
Current problems
Cloud App Security frequently generates false positive alerts when users connect to both offices simultaneously.
Planned Changes
Litware plans to implement the following changes:
Create and configure Azure Sentinel in the Azure subscription.
Validate Azure Sentinel functionality by using Azure AD test user accounts.
Business Requirements
Litware identifies the following business requirements:




Azure Information Protection Requirements
All files that have security labels and are stored on the Windows 10 computers must be available from the Azure Information Protection - Data discovery dashboard.
Microsoft Defender for Endpoint Requirements
All Cloud App Security unsanctioned apps must be blocked on the Windows 10 computers by using Microsoft Defender for Endpoint.
Microsoft Cloud App Security Requirements
Cloud App Security must identify whether a user connection is anomalous based on tenant-level data.
Azure Defender Requirements
All servers must send logs to the same Log Analytics workspace.
Azure Sentinel Requirements
Litware must meet the following Azure Sentinel requirements:
Integrate Azure Sentinel and Cloud App Security.
Ensure that a user named admin1 can configure Azure Sentinel playbooks.
Create an Azure Sentinel analytics rule based on a custom query. The rule must automatically initiate the execution of a playbook.
Add notes to events that represent data access from a specific IP address to provide the ability to reference the IP address when navigating through an investigation graph while hunting.
Create a test rule that generates alerts when inbound access to Microsoft Office 365 by the Azure AD test user accounts is detected. Alerts generated by the rule must be grouped into individual incidents, with one incident per test user account.
Existing Environment
Identity Environment
The network contains an Active Directory forest named litware.com that syncs to an Azure Active Directory (Azure AD) tenant named litware.com.
Microsoft 365 Environment
Litware has a Microsoft 365 E5 subscription linked to the litware.com Azure AD tenant. Microsoft Defender for Endpoint is deployed to all computers that run Windows 10. All Microsoft Cloud App Security built-in anomaly detection policies are enabled.
Azure Environment
Litware has an Azure subscription linked to the litware.com Azure AD tenant. The subscription contains resources in the East US Azure region as shown in the following table.
Network Environment
Each Litware office connects directly to the internet and has a site-to-site VPN connection to the virtual networks in the Azure subscription.
On-premises Environment
The on-premises network contains the computers shown in the following table.
Current problems
Cloud App Security frequently generates false positive alerts when users connect to both offices simultaneously.
Planned Changes
Litware plans to implement the following changes:
Create and configure Azure Sentinel in the Azure subscription.
Validate Azure Sentinel functionality by using Azure AD test user accounts.
Business Requirements
Litware identifies the following business requirements:




Azure Information Protection Requirements
All files that have security labels and are stored on the Windows 10 computers must be available from the Azure Information Protection - Data discovery dashboard.
Microsoft Defender for Endpoint Requirements
All Cloud App Security unsanctioned apps must be blocked on the Windows 10 computers by using Microsoft Defender for Endpoint.
Microsoft Cloud App Security Requirements
Cloud App Security must identify whether a user connection is anomalous based on tenant-level data.
Azure Defender Requirements
All servers must send logs to the same Log Analytics workspace.
Azure Sentinel Requirements
Litware must meet the following Azure Sentinel requirements:
Integrate Azure Sentinel and Cloud App Security.
Ensure that a user named admin1 can configure Azure Sentinel playbooks.
Create an Azure Sentinel analytics rule based on a custom query. The rule must automatically initiate the execution of a playbook.
Add notes to events that represent data access from a specific IP address to provide the ability to reference the IP address when navigating through an investigation graph while hunting.
Create a test rule that generates alerts when inbound access to Microsoft Office 365 by the Azure AD test user accounts is detected. Alerts generated by the rule must be grouped into individual incidents, with one incident per test user account.
- Question List (171q)
- Question 1: You have a Microsoft 365 E5 subscription. You plan to perfor...
- 1 commentQuestion 2: You need to implement Microsoft Defender for Cloud to meet t...
- 1 commentQuestion 3: You have an Azure Sentinel deployment. You need to query for...
- Question 4: You have a Microsoft 365 E5 subscription. You plan to perfor...
- 1 commentQuestion 5: You have an Azure subscription that contains 100 Linux virtu...
- 1 commentQuestion 6: You use Azure Sentinel. You need to receive an immediate ale...
- Question 7: You need to add notes to the events to meet the Azure Sentin...
- Question 8: You need to add notes to the events to meet the Azure Sentin...
- 1 commentQuestion 9: You have the following KQL query. (Exhibit)...
- 1 commentQuestion 10: You have an Azure subscription that contains a Log Analytics...
- Question 11: Note: This question is part of a series of questions that pr...
- 1 commentQuestion 12: You have an Azure subscription linked to an Azure Active Dir...
- 1 commentQuestion 13: From Azure Sentinel, you open the Investigation pane for a h...
- Question 14: You need to create a query for a workbook. The query must me...
- Question 15: You deploy Azure Sentinel. You need to implement connectors ...
- Question 16: You need to implement the Azure Information Protection requi...
- 1 commentQuestion 17: You have the resources shown in the following table. (Exhibi...
- 1 commentQuestion 18: You have a Microsoft Sentinel workspace named Workspaces You...
- 1 commentQuestion 19: DRAG DROP You plan to connect an external solution that will...
- 1 commentQuestion 20: Your company uses Azure Sentinel. A new security analyst rep...
- Question 21: You need to create the test rule to meet the Azure Sentinel ...
- Question 22: You need to recommend a solution to meet the technical requi...
- Question 23: You manage the security posture of an Azure subscription tha...
- 1 commentQuestion 24: You need to remediate active attacks to meet the technical r...
- Question 25: Note: This question is part of a series of questions that pr...
- 1 commentQuestion 26: You have an Azure subscription that uses Azure Defender. You...
- 1 commentQuestion 27: You have a playbook in Azure Sentinel. When you trigger the ...
- Question 28: You have an Azure subscription linked to an Azure Active Dir...
- 1 commentQuestion 29: You are configuring Azure Sentinel. You need to send a Micro...
- 1 commentQuestion 30: You have an Azure subscription. You plan to implement an Mic...
- Question 31: You need to create a query for a workbook. The query must me...
- Question 32: A company wants to analyze by using Microsoft 365 Apps. You ...
- Question 33: You need to create a query for a workbook. The query must me...
- 1 commentQuestion 34: You have an Azure subscription. The subscription contains 10...
- 1 commentQuestion 35: You have an Azure subscription that uses Microsoft Defender ...
- 1 commentQuestion 36: You need to configure the Azure Sentinel integration to meet...
- Question 37: You need to remediate active attacks to meet the technical r...
- 1 commentQuestion 38: You are informed of a new common vulnerabilities and exposur...
- Question 39: HOTSPOT You need to implement Azure Defender to meet the Azu...
- 1 commentQuestion 40: You have a Microsoft Sentinel workspace You develop a custom...
- 1 commentQuestion 41: You have a Microsoft Sentinel workspace that contains the fo...
- Question 42: You need to implement Azure Defender to meet the Azure Defen...
- 1 commentQuestion 43: Your on-premises network contains 100 servers that run Windo...
- 1 commentQuestion 44: Note: This question is part of a series of questions that pr...
- 1 commentQuestion 45: You have the following advanced hunting query in Microsoft 3...
- Question 46: You need to recommend a solution to meet the technical requi...
- Question 47: You have a Microsoft Sentinel workspace. You need to create ...
- Question 48: You are informed of an increase in malicious email being rec...
- Question 49: You need to use an Azure Sentinel analytics rule to search f...
- 1 commentQuestion 50: You need to create an advanced hunting query to investigate ...
- Question 51: You need to create a query for a workbook. The query must me...
- Question 52: You are informed of a new common vulnerabilities and exposur...
- 1 commentQuestion 53: You purchase a Microsoft 365 subscription. You plan to confi...
- Question 54: You are informed of a new common vulnerabilities and exposur...
- 1 commentQuestion 55: You use Azure Sentinel to monitor irregular Azure activity. ...
- Question 56: You use Microsoft Sentinel. You need to receive an alert in ...
- Question 57: You are informed of a new common vulnerabilities and exposur...
- 1 commentQuestion 58: You need to configure the Azure Sentinel integration to meet...
- Question 59: You need to recommend remediation actions for the Azure Defe...
- Question 60: HOTSPOT You have a Microsoft 365 E5 subscription. You plan t...
- Question 61: You have a Microsoft Sentinel workspace named sws1. You need...
- Question 62: You have the following advanced hunting query in Microsoft 3...
- Question 63: You need to configure the Azure Sentinel integration to meet...
- Question 64: You have a Microsoft Sentinel workspace named sws1. You need...
- Question 65: You have an Azure subscription that uses Microsoft Defender ...
- Question 66: You use Azure Sentinel to monitor irregular Azure activity. ...
- 1 commentQuestion 67: You implement Safe Attachments policies in Microsoft Defende...
- 1 commentQuestion 68: You need to modify the anomaly detection policy settings to ...
- Question 69: HOTSPOT You need to create an advanced hunting query to inve...
- 1 commentQuestion 70: You are investigating an incident by using Microsoft 365 Def...
- 1 commentQuestion 71: You have a Microsoft 365 subscription that uses Microsoft De...
- Question 72: You need to create the analytics rule to meet the Azure Sent...
- 1 commentQuestion 73: You need to remediate active attacks to meet the technical r...
- 1 commentQuestion 74: The issue for which team can be resolved by using Microsoft ...
- 1 commentQuestion 75: You have an Azure subscription that uses Microsoft Sentinel....
- 1 commentQuestion 76: Your company has a single office in Istanbul and a Microsoft...
- Question 77: You need to implement Azure Defender to meet the Azure Defen...
- Question 78: You create an Azure subscription named sub1. In sub1, you cr...
- Question 79: You need to create a query for a workbook. The query must me...
- 1 commentQuestion 80: You need to restrict cloud apps running on CLIENT1 to meet t...
- Question 81: A company uses Azure Sentinel. You need to create an automat...
- 1 commentQuestion 82: You have an Azure subscription. You need to delegate permiss...
- 1 commentQuestion 83: You have an Azure Storage account that will be accessed by m...
- Question 84: You have a Microsoft Sentinel workspace named Workspaces You...
- Question 85: You have a Microsoft Sentinel workspace. You need to create ...
- 1 commentQuestion 86: You have an Azure Sentinel workspace. You need to test a pla...
- 1 commentQuestion 87: Your company uses line-of-business apps that contain Microso...
- 3 commentQuestion 88: You need to minimize the effort required to investigate the ...
- Question 89: You need to recommend a solution to meet the technical requi...
- 1 commentQuestion 90: You are configuring Microsoft Cloud App Security. You have a...
- 1 commentQuestion 91: Your company deploys Azure Sentinel. You plan to delegate th...
- Question 92: You have an Azure Sentinel workspace. You need to test a pla...
- Question 93: You have a Microsoft 365 E5 subscription. You plan to perfor...
- 1 commentQuestion 94: You have the following SQL query. (Exhibit)...
- 1 commentQuestion 95: You need to implement Azure Sentinel queries for Contoso and...
- 1 commentQuestion 96: You provision Azure Sentinel for a new Azure subscription. Y...
- 1 commentQuestion 97: You have the resources shown in the following table. (Exhibi...
- Question 98: You have an Azure subscription that uses Azure Defender. You...
- 1 commentQuestion 99: Your company has an on-premises network that uses Microsoft ...
- 1 commentQuestion 100: Note: This question is part of a series of questions that pr...
- Question 101: You need to use an Azure Resource Manager template to create...
- Question 102: You have a Microsoft 365 E5 subscription that uses Microsoft...
- Question 103: You need to create the analytics rule to meet the Azure Sent...
- 1 commentQuestion 104: You have the resources shown in the following table. (Exhibi...
- Question 105: You create a new Azure subscription and start collecting log...
- 1 commentQuestion 106: You are investigating an incident by using Microsoft 365 Def...
- Question 107: You have the following SQL query. (Exhibit)...
- 1 commentQuestion 108: You need to complete the query for failed sign-ins to meet t...
- 1 commentQuestion 109: You open the Cloud App Security portal as shown in the follo...
- Question 110: You need to remediate active attacks to meet the technical r...
- Question 111: Note: This question is part of a series of questions that pr...
- Question 112: You manage the security posture of an Azure subscription tha...
- 1 commentQuestion 113: Your company stores the data for every project in a differen...
- 1 commentQuestion 114: You use Azure Sentinel to monitor irregular Azure activity. ...
- Question 115: You implement Safe Attachments policies in Microsoft Defende...
- Question 116: Your company deploys Azure Sentinel. You plan to delegate th...
- Question 117: You need to create the analytics rule to meet the Azure Sent...
- Question 118: You have a Microsoft 365 E5 subscription that uses Microsoft...
- 1 commentQuestion 119: You need to visualize Azure Sentinel data and enrich the dat...
- 1 commentQuestion 120: You need to configure the Microsoft Sentinel integration to ...
- Question 121: You need to create the analytics rule to meet the Azure Sent...
- Question 122: Your company deploys Azure Sentinel. You plan to delegate th...
- 1 commentQuestion 123: You recently deployed Azure Sentinel. You discover that the ...
- Question 124: You need to use an Azure Sentinel analytics rule to search f...
- Question 125: HOTSPOT You have a Microsoft 365 E5 subscription that uses M...
- Question 126: You use Azure Sentinel to monitor irregular Azure activity. ...
- Question 127: You have a Microsoft 365 subscription that uses Microsoft 36...
- Question 128: You receive a security bulletin about a potential attack tha...
- Question 129: You have a Microsoft 365 E5 subscription. You plan to perfor...
- 1 commentQuestion 130: You have a Microsoft 365 E5 subscription that contains two u...
- Question 131: You have a Microsoft Sentinel workspace named Workspaces You...
- Question 132: Your company uses Azure Sentinel. A new security analyst rep...
- Question 133: You have an Azure subscription that has Azure Defender enabl...
- Question 134: You need to implement Azure Sentinel queries for Contoso and...
- Question 135: You are configuring Microsoft Cloud App Security. You have a...
- 1 commentQuestion 136: You use Azure Sentinel to monitor irregular Azure activity. ...
- Question 137: You have a Microsoft Sentinel workspace You develop a custom...
- Question 138: You need to implement Azure Defender to meet the Azure Defen...
- 1 commentQuestion 139: You have an Azure subscription that has Azure Defender enabl...
- Question 140: You need to recommend remediation actions for the Azure Defe...
- 1 commentQuestion 141: You have five on-premises Linux servers. You have an Azure s...
- 2 commentQuestion 142: You need to configure DC1 to meet the business requirements....
- 1 commentQuestion 143: Note: This question is part of a series of questions that pr...
- Question 144: Note: This question is part of a series of questions that pr...
- 1 commentQuestion 145: You need to modify the anomaly detection policy settings to ...
- 1 commentQuestion 146: You have an Azure subscription. You need to delegate permiss...
- 1 commentQuestion 147: You have an Azure subscription that uses Azure Defender. You...
- 1 commentQuestion 148: You create an Azure subscription. You enable Azure Defender ...
- Question 149: The issue for which team can be resolved by using Microsoft ...
- Question 150: HOTSPOT You need to use an Azure Resource Manager template t...
- Question 151: DRAG DROP You need to configure DC1 to meet the business req...
- Question 152: You are investigating a potential attack that deploys a new ...
- Question 153: You provision a Linux virtual machine in a new Azure subscri...
- 1 commentQuestion 154: You have resources in Azure and Google cloud. You need to in...
- 1 commentQuestion 155: You need to configure the Azure Sentinel integration to meet...
- Question 156: You have an Azure subscription that has Azure Defender enabl...
- Question 157: You use Azure Sentinel to monitor irregular Azure activity. ...
- Question 158: You create a new Azure subscription and start collecting log...
- Question 159: You need to recommend remediation actions for the Azure Defe...
- Question 160: You have a Microsoft 365 subscription that uses Microsoft 36...
- Question 161: HOTSPOT You are informed of an increase in malicious email b...
- 1 commentQuestion 162: You have an Azure Storage account that will be accessed by m...
- Question 163: Your company uses Microsoft Sentinel A new security analyst ...
- 1 commentQuestion 164: You have a Microsoft subscription that has Microsoft Defende...
- 1 commentQuestion 165: You have a Microsoft Sentinel workspace. You need to prevent...
- Question 166: You plan to connect an external solution that will send Comm...
- Question 167: The issue for which team can be resolved by using Microsoft ...
- 1 commentQuestion 168: You have two Azure subscriptions that use Microsoft Defender...
- 1 commentQuestion 169: You have the following environment: Azure Sentinel A Microso...
- 1 commentQuestion 170: You have a Microsoft Sentinel workspace. You have a query na...
- Question 171: You create a new Azure subscription and start collecting log...



Recent Comments (The most recent comments are at the top.)
Selected Answer: AB
A - this seems correct, as if you override the automatic detection of location for company IP address ranges, you can prevent the impossible travel alerts.
B - This makes sense as you need to define your corporate address ranges so that they are not seen as risky.
C - Increasing the sensitivity of the impossible travel detection would create more alerts.
D - Why would you set the IP addresses to the "Other" category when there is a "Corporate" category that fits the description?
E - Creating a new policy when there is already an existing one that you need to reduce the alerts from, would not reduce the number of alerts.