Valid SY0-601 Dumps shared by ExamDiscuss.com for Helping Passing SY0-601 Exam! ExamDiscuss.com now offer the newest SY0-601 exam dumps, the ExamDiscuss.com SY0-601 exam questions have been updated and answers have been corrected get the newest ExamDiscuss.com SY0-601 dumps with Test Engine here:
Access SY0-601 Dumps Premium Version
(1061 Q&As Dumps, 35%OFF Special Discount Code: freecram)
<< Prev Question Next Question >>
Question 74/139
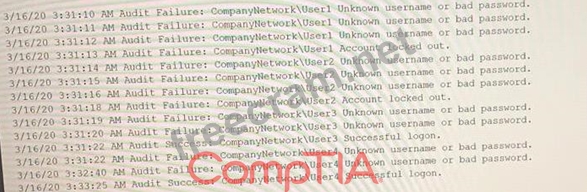
A security analyst needs to determine how an attacker was able to use User3 to gain a foothold within a company's network. The company's lockout policy requires that an account be locked out for a minimum of 15 minutes after three unsuccessful attempts. While reviewing the log files, the analyst discovers the following:
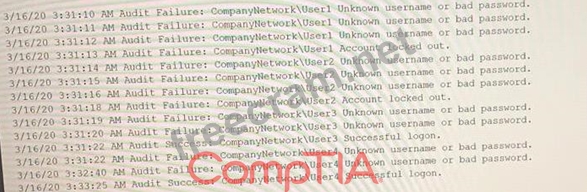
Which of the following attacks MOST likely occurred?
Which of the following attacks MOST likely occurred?
Correct Answer: D
- Question List (139q)
- Question 1: In which of the following situations would it be BEST to use...
- Question 2: An.. that has a large number of mobile devices is exploring ...
- Question 3: A security analyst needs to be proactive in understand the t...
- Question 4: A development team employs a practice of bringing all the co...
- Question 5: A small company that does not have security staff wants to i...
- Question 6: A network administrator is concerned about users being expos...
- Question 7: In the middle of a cybersecurity, a security engineer remove...
- Question 8: A security auditor is reviewing vulnerability scan data prov...
- Question 9: A company recently experienced an attack in which a maliciou...
- Question 10: To secure an application after a large data breach, an e-com...
- Question 11: A security engineer needs to enhance MFA access to sensitive...
- Question 12: Which of the following types of controls is a turnstile?...
- Question 13: After a phishing scam for a user's credentials, the red team...
- Question 14: A security administrator needs to create a RAIS configuratio...
- Question 15: Which of the following cloud models provides clients with se...
- Question 16: A security engineer needs to implement an MDM solution that ...
- Question 17: Ann, a forensic analyst, needs to prove that the data she or...
- Question 18: A financial analyst is expecting an email containing sensiti...
- Question 19: An organization recently acquired an ISO 27001 certification...
- Question 20: A user is concerned that a web application will not be able ...
- Question 21: An organization is developing an authentication service for ...
- Question 22: A cybersecurity administrator is using iptables as an enterp...
- Question 23: When selecting a technical solution for identity management,...
- Question 24: While reviewing the wireless router, the systems administrat...
- Question 25: An attacked is attempting to exploit users by creating a fak...
- Question 26: The spread of misinformation surrounding the outbreak of a n...
- Question 27: A security analyst sees the following log output while revie...
- Question 28: A major clothing company recently lost a large amount of pro...
- Question 29: A security analyst must determine if either SSH or Telnet is...
- Question 30: The following are the logs of a successful attack. (Exhibit)...
- Question 31: A Chief Security Officer (CSO) was notified that a customer ...
- Question 32: A company recently added a DR site and is redesigning the ne...
- Question 33: A document that appears to be malicious has been discovered ...
- Question 34: Phone number, address, and date of birth be provided to conf...
- Question 35: The cost of 'movable media and the security risks of transpo...
- Question 36: A security analyst discovers several .jpg photos from a cell...
- Question 37: An end user reports a computer has been acting slower than n...
- Question 38: During an incident response, a security analyst observes the...
- Question 39: A security administrator is trying to determine whether a se...
- Question 40: A cybersecurity analyst reviews the log files from a web ser...
- Question 41: Which of the following is the purpose of a risk register?...
- Question 42: Which of the following is the correct order of volatility fr...
- Question 43: The IT department's on-site developer has been with the team...
- Question 44: An organization has expanded its operations by opening a rem...
- Question 45: A security analyst is reviewing information regarding recent...
- Question 46: A security analyst is performing a packet capture on a serie...
- Question 47: A financial organization has adopted a new secure, encrypted...
- Question 48: An organization just experienced a major cyberattack modem. ...
- Question 49: A network administrator would like to configure a site-to-si...
- Question 50: Which of the following terms should be included in a contrac...
- Question 51: A company is launching a new internet platform for its clien...
- Question 52: Several employees return to work the day after attending an ...
- Question 53: A systems administrator needs to install a new wireless netw...
- Question 54: A network administrator has been alerted that web pages are ...
- Question 55: A security engineer at an offline government facility is con...
- Question 56: A security analyst has received an alert about being sent vi...
- Question 57: A web server administrator has redundant servers and needs t...
- Question 58: An enterprise needs to keep cryptographic keys in a safe man...
- Question 59: After consulting with the Chief Risk Officer (CRO). a manage...
- Question 60: An organization routes all of its traffic through a VPN Most...
- Question 61: Phishing and spear-phishing attacks have been occurring more...
- Question 62: A company recently set up an e-commerce portal to sell its p...
- Question 63: A remote user recently took a two-week vacation abroad and b...
- Question 64: n organization plans to transition the intrusion detection a...
- Question 65: A security administrator currently spends a large amount of ...
- Question 66: Which of the following is the BEST reason to maintain a func...
- Question 67: An analyst visits an internet forum looking for information ...
- Question 68: A network engineer has been asked to investigate why several...
- Question 69: A company is adopting a BYOD policy and is looking for a com...
- Question 70: A network engineer needs to build a solution that will allow...
- Question 71: The website http://companywebsite.com requires users to prov...
- Question 72: A small business just recovered from a ransomware attack aga...
- Question 73: A network administrator has been asked to install an IDS to ...
- Question 74: A security analyst needs to determine how an attacker was ab...
- Question 75: A company's Chief Information Office (CIO) is meeting with t...
- Question 76: A security analyst is investigating an incident to determine...
- Question 77: A company needs to centralize its logs to create a baseline ...
- Question 78: A Chief Executive Officer (CEO) is dissatisfied with the lev...
- Question 79: A security analyst is investigating a vulnerability in which...
- Question 80: A security analyst reviews the datacenter access logs for a ...
- Question 81: A university is opening a facility in a location where there...
- Question 82: A large financial services firm recently released informatio...
- Question 83: A company recently moved sensitive videos between on-premise...
- Question 84: A company recently transitioned to a strictly BYOD culture d...
- Question 85: A network administrator at a large organization Is reviewing...
- Question 86: Which of the following often operates in a client-server arc...
- Question 87: Which of the following scenarios BEST describes a risk reduc...
- Question 88: Which of the following would be BEST to establish between or...
- Question 89: A company is upgrading its wireless infrastructure to WPA2-E...
- Question 90: Following a prolonged datacenter outage that affected web-ba...
- Question 91: Which of the following would be BEST for a technician to rev...
- Question 92: A forensics examiner is attempting to dump password cached i...
- Question 93: An incident, which is affecting dozens of systems, involves ...
- Question 94: A user enters a password to log in to a workstation and is t...
- Question 95: A security assessment determines DES and 3DES at still being...
- Question 96: An organization hired a consultant to assist with an active ...
- Question 97: A smart retail business has a local store and a newly establ...
- Question 98: Which of the following scenarios would make a DNS sinkhole e...
- Question 99: A company provides mobile devices to its users to permit acc...
- Question 100: Which of the following incident response steps involves acti...
- Question 101: During a routine scan of a wireless segment at a retail comp...
- Question 102: The manager who is responsible for a data set has asked a se...
- Question 103: A forensics investigator is examining a number of unauthoriz...
- Question 104: A security engineer has enabled two-factor authentication on...
- Question 105: An organization has decided to host its web application and ...
- Question 106: On which of the following is the live acquisition of data fo...
- Question 107: A root cause analysis reveals that a web application outage ...
- Question 108: Which of the following policies would help an organization i...
- Question 109: A commercial cyber-threat intelligence organization observes...
- Question 110: The facilities supervisor for a government agency is concern...
- Question 111: A network engineer needs to create a plan for upgrading the ...
- Question 112: An organization suffered an outage and a critical system too...
- Question 113: An attacker was easily able to log in to a company's securit...
- Question 114: A security administrator is setting up a SIEM to help monito...
- Question 115: A network administrator has been asked to design a solution ...
- Question 116: A vulnerability assessment report will include the CVSS scor...
- Question 117: An organization recently recovered from a data breach. Durin...
- Question 118: A nationwide company is experiencing unauthorized logins at ...
- Question 119: A recent audit uncovered a key finding regarding the use of ...
- Question 120: An auditor is performing an assessment of a security applian...
- Question 121: Users have been issued smart cards that provide physical acc...
- Question 122: A startup company is using multiple SaaS and IaaS platform t...
- Question 123: A cybersecurity administrator has a reduced team and needs t...
- Question 124: A researcher has been analyzing large data sets for the last...
- Question 125: After entering a username and password, and administrator mu...
- Question 126: Which of the following provides the BEST protection for sens...
- Question 127: A startup company is using multiple SaaS and IaaS platforms ...
- Question 128: Under GDPR, which of the following is MOST responsible for t...
- Question 129: A security analyst needs to make a recommendation for restri...
- Question 130: While checking logs, a security engineer notices a number of...
- Question 131: A well-known organization has been experiencing attacks from...
- Question 132: An organization's RPO for a critical system is two hours. Th...
- Question 133: Which of the following are the MOST likely vectors for the u...
- Question 134: The website http://companywebsite.com requires users to prov...
- Question 135: Which of the following utilize a subset of real data and are...
- Question 136: Which of the following distributes data among nodes, making ...
- Question 137: Which of the following would be the BEST resource lor a soft...
- Question 138: A company's Chief Information Security Officer (CISO) recent...
- Question 139: An organization has hired a security analyst to perform a pe...


